Search Results for author: Yujie Chen
Found 9 papers, 2 papers with code
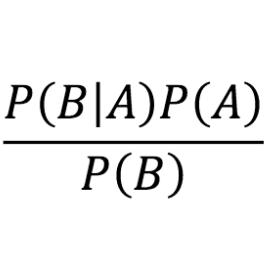
Likelihood Based Inference in Fully and Partially Observed Exponential Family Graphical Models with Intractable Normalizing Constants
1 code implementation • 27 Apr 2024 • Yujie Chen, Anindya Bhadra, Antik Chakraborty
Probabilistic graphical models that encode an underlying Markov random field are fundamental building blocks of generative modeling to learn latent representations in modern multivariate data sets with complex dependency structures.
Dr3: Ask Large Language Models Not to Give Off-Topic Answers in Open Domain Multi-Hop Question Answering
no code implementations • 19 Mar 2024 • Yuan Gao, Yiheng Zhu, Yuanbin Cao, Yinzhi Zhou, Zhen Wu, Yujie Chen, Shenglan Wu, Haoyuan Hu, Xinyu Dai
To alleviate this issue, we propose the Discriminate->Re-Compose->Re- Solve->Re-Decompose (Dr3) mechanism.
Progressive Distillation Based on Masked Generation Feature Method for Knowledge Graph Completion
1 code implementation • 19 Jan 2024 • Cunhang Fan, Yujie Chen, Jun Xue, Yonghui Kong, JianHua Tao, Zhao Lv
This paper proposes a progressive distillation method based on masked generation features for KGC task, aiming to significantly reduce the complexity of pre-trained models.
Learning to Denoise Unreliable Interactions for Link Prediction on Biomedical Knowledge Graph
no code implementations • 9 Dec 2023 • Tengfei Ma, Yujie Chen, Wen Tao, Dashun Zheng, Xuan Lin, Patrick Cheong-lao Pang, Yiping Liu, Yijun Wang, Bosheng Song, Xiangxiang Zeng
By maximizing the mutual information between the reliable structure and smoothed semantic relations, DenoisedLP emphasizes the informative interactions for predicting relation-specific links.
Enhancing Low-Precision Sampling via Stochastic Gradient Hamiltonian Monte Carlo
no code implementations • 25 Oct 2023 • Ziyi Wang, Yujie Chen, Qifan Song, Ruqi Zhang
This paper investigates low-precision sampling via Stochastic Gradient Hamiltonian Monte Carlo (SGHMC) with low-precision and full-precision gradient accumulators for both strongly log-concave and non-log-concave distributions.
Multi-perspective Information Fusion Res2Net with RandomSpecmix for Fake Speech Detection
no code implementations • 27 Jun 2023 • Shunbo Dong, Jun Xue, Cunhang Fan, Kang Zhu, Yujie Chen, Zhao Lv
The main purpose of this system is to improve the model's ability to learn precise forgery information for FSD task in low-quality scenarios.
An Online Algorithm for Chance Constrained Resource Allocation
no code implementations • 6 Mar 2023 • Yuwei Chen, Zengde Deng, Yinzhi Zhou, Zaiyi Chen, Yujie Chen, Haoyuan Hu
This paper studies the online stochastic resource allocation problem (RAP) with chance constraints.
Bio-Inspired Adversarial Attack Against Deep Neural Networks
no code implementations • 30 Jun 2021 • Bowei Xi, Yujie Chen, Fan Fei, Zhan Tu, Xinyan Deng
Hence in a successful physical attack against DNN, targeted motion against the system should also be considered.
Can Sophisticated Dispatching Strategy Acquired by Reinforcement Learning? - A Case Study in Dynamic Courier Dispatching System
no code implementations • 7 Mar 2019 • Yujie Chen, Yu Qian, Yichen Yao, Zili Wu, Rongqi Li, Yinzhi Zhou, Haoyuan Hu, Yinghui Xu
In this paper, we study a courier dispatching problem (CDP) raised from an online pickup-service platform of Alibaba.