Search Results for author: Xinyi Hu
Found 10 papers, 2 papers with code
Version age-based client scheduling policy for federated learning
no code implementations • 8 Feb 2024 • Xinyi Hu, Nikolaos Pappas, Howard H. Yang
Motivated by this, we introduce the novel concept of Version Age of Information (VAoI) to FL.
Two-Stage Predict+Optimize for Mixed Integer Linear Programs with Unknown Parameters in Constraints
1 code implementation • 14 Nov 2023 • Xinyi Hu, Jasper C. H. Lee, Jimmy H. M. Lee
We also give a training algorithm usable for all mixed integer linear programs, vastly generalizing the applicability of the framework.
Learning Mutually Informed Representations for Characters and Subwords
no code implementations • 14 Nov 2023 • Yilin Wang, Xinyi Hu, Matthew R. Gormley
In this paper, we introduce the entanglement model, aiming to combine character and subword language models.
Branch & Learn with Post-hoc Correction for Predict+Optimize with Unknown Parameters in Constraints
no code implementations • 12 Mar 2023 • Xinyi Hu, Jasper C. H. Lee, Jimmy H. M. Lee
Combining machine learning and constrained optimization, Predict+Optimize tackles optimization problems containing parameters that are unknown at the time of solving.
Predict+Optimize for Packing and Covering LPs with Unknown Parameters in Constraints
no code implementations • 8 Sep 2022 • Xinyi Hu, Jasper C. H. Lee, Jimmy H. M. Lee
First, we propose a novel and practically relevant framework for the Predict+Optimize setting, but with unknown parameters in both the objective and the constraints.
Branch & Learn for Recursively and Iteratively Solvable Problems in Predict+Optimize
no code implementations • 1 May 2022 • Xinyi Hu, Jasper C. H. Lee, Jimmy H. M. Lee, Allen Z. Zhong
This paper proposes Branch & Learn, a framework for Predict+Optimize to tackle optimization problems containing parameters that are unknown at the time of solving.
Reinforcement Learning for Predict+Optimize
no code implementations • CUHK Course IERG5350 2020 • Xinyi Hu, Yuansen Cheng
Predict+Optimize (P+O) is a machine learning framework for optimization problems with unknown parameters.
"Drunk Man" Saves Our Lives: Route Planning by a Biased Random Walk Mode
no code implementations • 4 Oct 2020 • Xinyi Hu, Quchen Miao, Zexuan Zhao
Based on the hurricane striking Puerto Rico in 2017, we developed a transportable disaster response system "DroneGo" featuring a drone fleet capable of delivering the medical package and videoing roads.
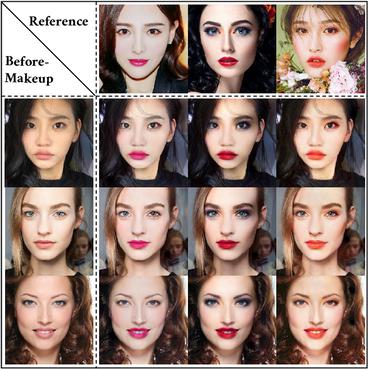
Compressing Facial Makeup Transfer Networks by Collaborative Distillation and Kernel Decomposition
1 code implementation • 16 Sep 2020 • Bianjiang Yang, Zi Hui, Haoji Hu, Xinyi Hu, Lu Yu
Although the facial makeup transfer network has achieved high-quality performance in generating perceptually pleasing makeup images, its capability is still restricted by the massive computation and storage of the network architecture.
A Mixture Model Based Defense for Data Poisoning Attacks Against Naive Bayes Spam Filters
no code implementations • 31 Oct 2018 • David J. Miller, Xinyi Hu, Zhen Xiang, George Kesidis
Such attacks are successful mainly because of the poor representation power of the naive Bayes (NB) model, with only a single (component) density to represent spam (plus a possible attack).