Search Results for author: Tugba Erpek
Found 38 papers, 0 papers with code
Will 6G be Semantic Communications? Opportunities and Challenges from Task Oriented and Secure Communications to Integrated Sensing
no code implementations • 3 Jan 2024 • Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
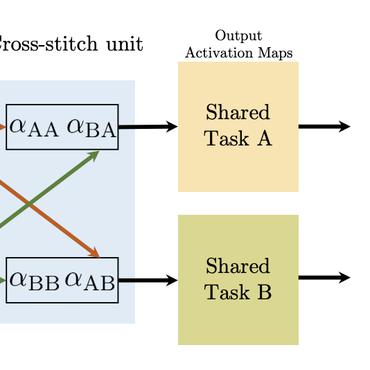
This paper explores opportunities and challenges of task (goal)-oriented and semantic communications for next-generation (NextG) communication networks through the integration of multi-task learning.
Securing NextG Systems against Poisoning Attacks on Federated Learning: A Game-Theoretic Solution
no code implementations • 28 Dec 2023 • Yalin E. Sagduyu, Tugba Erpek, Yi Shi
This paper studies the poisoning attack and defense interactions in a federated learning (FL) system, specifically in the context of wireless signal classification using deep learning for next-generation (NextG) communications.
Adversarial Attacks on LoRa Device Identification and Rogue Signal Detection with Deep Learning
no code implementations • 27 Dec 2023 • Yalin E. Sagduyu, Tugba Erpek
Results presented in this paper quantify the level of transferability of adversarial attacks on different LoRa signal classification tasks as a major vulnerability and highlight the need to make IoT applications robust to adversarial attacks.
Joint Sensing and Task-Oriented Communications with Image and Wireless Data Modalities for Dynamic Spectrum Access
no code implementations • 21 Dec 2023 • Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
Recognizing the computational constraints and trust issues associated with on-device computation, we propose a collaborative system wherein the edge device communicates selectively processed information to a trusted receiver acting as a fusion center, where a decision is made to identify whether a potential transmitter is present, or not.
Learning-Based UAV Path Planning for Data Collection with Integrated Collision Avoidance
no code implementations • 11 Dec 2023 • Xueyuan Wang, M. Cenk Gursoy, Tugba Erpek, Yalin E. Sagduyu
Unmanned aerial vehicles (UAVs) are expected to be an integral part of wireless networks, and determining collision-free trajectory in multi-UAV non-cooperative scenarios while collecting data from distributed Internet of Things (IoT) nodes is a challenging task.
Joint Sensing and Semantic Communications with Multi-Task Deep Learning
no code implementations • 8 Nov 2023 • Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
The transmitter employs a deep neural network, namely an encoder, for joint operations of source coding, channel coding, and modulation, while the receiver utilizes another deep neural network, namely a decoder, for joint operations of demodulation, channel decoding, and source decoding to reconstruct the data samples.
Multi-Receiver Task-Oriented Communications via Multi-Task Deep Learning
no code implementations • 14 Aug 2023 • Yalin E. Sagduyu, Tugba Erpek, Aylin Yener, Sennur Ulukus
A multi-task deep learning approach that involves training a common encoder at the transmitter and individual decoders at the receivers is presented for joint optimization of completing multiple tasks and communicating with multiple receivers.
Jamming Attacks on Decentralized Federated Learning in General Multi-Hop Wireless Networks
no code implementations • 12 Jan 2023 • Yi Shi, Yalin E. Sagduyu, Tugba Erpek
We show that the DFL performance can be significantly reduced by jamming attacks launched in a wireless network and characterize the attack surface as a vulnerability study before the safe deployment of DFL over wireless networks.
Vulnerabilities of Deep Learning-Driven Semantic Communications to Backdoor (Trojan) Attacks
no code implementations • 21 Dec 2022 • Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus, Aylin Yener
The backdoor attack can effectively change the semantic information transferred for the poisoned input samples to a target meaning.
Is Semantic Communications Secure? A Tale of Multi-Domain Adversarial Attacks
no code implementations • 20 Dec 2022 • Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus, Aylin Yener
By augmenting the reconstruction loss with a semantic loss, the two deep neural networks (DNNs) of this encoder-decoder pair are interactively trained with the DNN of the semantic task classifier.
Federated Learning for Distributed Spectrum Sensing in NextG Communication Networks
no code implementations • 6 Apr 2022 • Yi Shi, Yalin E. Sagduyu, Tugba Erpek
In this paper, distributed federated learning over a multi-hop wireless network is considered to collectively train a DNN for signal identification.
End-to-End Autoencoder Communications with Optimized Interference Suppression
no code implementations • 29 Dec 2021 • Kemal Davaslioglu, Tugba Erpek, Yalin E. Sagduyu
An end-to-end communications system based on Orthogonal Frequency Division Multiplexing (OFDM) is modeled as an autoencoder (AE) for which the transmitter (coding and modulation) and receiver (demodulation and decoding) are represented as deep neural networks (DNNs) of the encoder and decoder, respectively.
Covert Communications via Adversarial Machine Learning and Reconfigurable Intelligent Surfaces
no code implementations • 21 Dec 2021 • Brian Kim, Tugba Erpek, Yalin E. Sagduyu, Sennur Ulukus
Results from different network topologies show that adversarial perturbation and RIS interaction vector can be jointly designed to effectively increase the signal detection accuracy at the receiver while reducing the detection accuracy at the eavesdropper to enable covert communications.
Autoencoder-based Communications with Reconfigurable Intelligent Surfaces
no code implementations • 8 Dec 2021 • Tugba Erpek, Yalin E. Sagduyu, Ahmed Alkhateeb, Aylin Yener
This paper presents a novel approach for the joint design of a reconfigurable intelligent surface (RIS) and a transmitter-receiver pair that are trained together as a set of deep neural networks (DNNs) to optimize the end-to-end communication performance at the receiver.
Adversarial Attacks against Deep Learning Based Power Control in Wireless Communications
no code implementations • 16 Sep 2021 • Brian Kim, Yi Shi, Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus
The DNN that corresponds to a regression model is trained with channel gains as the input and returns transmit powers as the output.
Jamming-Resilient Path Planning for Multiple UAVs via Deep Reinforcement Learning
no code implementations • 9 Apr 2021 • Xueyuan Wang, M. Cenk Gursoy, Tugba Erpek, Yalin E. Sagduyu
Unmanned aerial vehicles (UAVs) are expected to be an integral part of wireless networks.
Adversarial Attacks on Deep Learning Based mmWave Beam Prediction in 5G and Beyond
no code implementations • 25 Mar 2021 • Brian Kim, Yalin E. Sagduyu, Tugba Erpek, Sennur Ulukus
Deep learning provides powerful means to learn from spectrum data and solve complex tasks in 5G and beyond such as beam selection for initial access (IA) in mmWave communications.
How to Attack and Defend NextG Radio Access Network Slicing with Reinforcement Learning
no code implementations • 14 Jan 2021 • Yi Shi, Yalin E. Sagduyu, Tugba Erpek, M. Cenk Gursoy
In this paper, reinforcement learning (RL) for network slicing is considered in NextG radio access networks, where the base station (gNodeB) allocates resource blocks (RBs) to the requests of user equipments and aims to maximize the total reward of accepted requests over time.
Networking and Internet Architecture
Adversarial Machine Learning for 5G Communications Security
no code implementations • 7 Jan 2021 • Yalin E. Sagduyu, Tugba Erpek, Yi Shi
For the second attack, the adversary spoofs wireless signals with the generative adversarial network (GAN) to infiltrate the physical layer authentication mechanism based on a deep learning classifier that is deployed at the 5G base station.
Deep Learning for Fast and Reliable Initial Access in AI-Driven 6G mmWave Networks
no code implementations • 6 Jan 2021 • Tarun S. Cousik, Vijay K. Shah, Tugba Erpek, Yalin E. Sagduyu, Jeffrey H. Reed
In LoS conditions, the selection of the beams is consequential and improves the accuracy by up to 70%.
Robust Improvement of the Age of Information by Adaptive Packet Coding
no code implementations • 9 Dec 2020 • Maice Costa, Yalin Sagduyu, Tugba Erpek, Muriel Médard
We consider a wireless communication network with an adaptive scheme to select the number of packets to be admitted and encoded for each transmission, and characterize the information timeliness.
Information Theory Information Theory H.1.1, E.4
Channel Effects on Surrogate Models of Adversarial Attacks against Wireless Signal Classifiers
no code implementations • 3 Dec 2020 • Brian Kim, Yalin E. Sagduyu, Tugba Erpek, Kemal Davaslioglu, Sennur Ulukus
The transmitter is equipped with a deep neural network (DNN) classifier for detecting the ongoing transmissions from the background emitter and transmits a signal if the spectrum is idle.
Reinforcement Learning for Dynamic Resource Optimization in 5G Radio Access Network Slicing
no code implementations • 14 Sep 2020 • Yi Shi, Yalin E. Sagduyu, Tugba Erpek
The paper presents a reinforcement learning solution to dynamic resource allocation for 5G radio access network slicing.
Adversarial Attacks with Multiple Antennas Against Deep Learning-Based Modulation Classifiers
no code implementations • 31 Jul 2020 • Brian Kim, Yalin E. Sagduyu, Tugba Erpek, Kemal Davaslioglu, Sennur Ulukus
First, we show that multiple independent adversaries, each with a single antenna cannot improve the attack performance compared to a single adversary with multiple antennas using the same total power.
Fast Initial Access with Deep Learning for Beam Prediction in 5G mmWave Networks
no code implementations • 22 Jun 2020 • Tarun S. Cousik, Vijay K. Shah, Jeffrey H. Reed, Tugba Erpek, Yalin E. Sagduyu
This paper presents DeepIA, a deep learning solution for faster and more accurate initial access (IA) in 5G millimeter wave (mmWave) networks when compared to conventional IA.
How to Make 5G Communications "Invisible": Adversarial Machine Learning for Wireless Privacy
no code implementations • 15 May 2020 • Brian Kim, Yalin E. Sagduyu, Kemal Davaslioglu, Tugba Erpek, Sennur Ulukus
We consider the problem of hiding wireless communications from an eavesdropper that employs a deep learning (DL) classifier to detect whether any transmission of interest is present or not.
Deep Learning for Wireless Communications
no code implementations • 12 May 2020 • Tugba Erpek, Timothy J. O'Shea, Yalin E. Sagduyu, Yi Shi, T. Charles Clancy
Existing communication systems exhibit inherent limitations in translating theory to practice when handling the complexity of optimization for emerging wireless applications with high degrees of freedom.
Channel-Aware Adversarial Attacks Against Deep Learning-Based Wireless Signal Classifiers
no code implementations • 11 May 2020 • Brian Kim, Yalin E. Sagduyu, Kemal Davaslioglu, Tugba Erpek, Sennur Ulukus
There is a transmitter that transmits signals with different modulation types.
Over-the-Air Adversarial Attacks on Deep Learning Based Modulation Classifier over Wireless Channels
no code implementations • 5 Feb 2020 • Brian Kim, Yalin E. Sagduyu, Kemal Davaslioglu, Tugba Erpek, Sennur Ulukus
In the meantime, the adversary makes over-the-air transmissions that are received as superimposed with the transmitter's signals to fool the classifier at the receiver into making errors.
When Wireless Security Meets Machine Learning: Motivation, Challenges, and Research Directions
no code implementations • 24 Jan 2020 • Yalin E. Sagduyu, Yi Shi, Tugba Erpek, William Headley, Bryse Flowers, George Stantchev, Zhuo Lu
Wireless systems are vulnerable to various attacks such as jamming and eavesdropping due to the shared and broadcast nature of wireless medium.
Adversarial Deep Learning for Over-the-Air Spectrum Poisoning Attacks
no code implementations • 1 Nov 2019 • Yalin E. Sagduyu, Yi Shi, Tugba Erpek
A transmitter applies deep learning on its spectrum sensing results to predict idle time slots for data transmission.
DeepWiFi: Cognitive WiFi with Deep Learning
no code implementations • 29 Oct 2019 • Kemal Davaslioglu, Sohraab Soltani, Tugba Erpek, Yalin E. Sagduyu
We present the DeepWiFi protocol, which hardens the baseline WiFi (IEEE 802. 11ac) with deep learning and sustains high throughput by mitigating out-of-network interference.
Real-Time and Embedded Deep Learning on FPGA for RF Signal Classification
no code implementations • 13 Oct 2019 • Sohraab Soltani, Yalin E. Sagduyu, Raqibul Hasan, Kemal Davaslioglu, Hongmei Deng, Tugba Erpek
We designed and implemented a deep learning based RF signal classifier on the Field Programmable Gate Array (FPGA) of an embedded software-defined radio platform, DeepRadio, that classifies the signals received through the RF front end to different modulation types in real time and with low power.
QoS and Jamming-Aware Wireless Networking Using Deep Reinforcement Learning
no code implementations • 13 Oct 2019 • Nof Abuzainab, Tugba Erpek, Kemal Davaslioglu, Yalin E. Sagduyu, Yi Shi, Sharon J. Mackey, Mitesh Patel, Frank Panettieri, Muhammad A. Qureshi, Volkan Isler, Aylin Yener
The problem of quality of service (QoS) and jamming-aware communications is considered in an adversarial wireless network subject to external eavesdropping and jamming attacks.
IoT Network Security from the Perspective of Adversarial Deep Learning
no code implementations • 31 May 2019 • Yalin E. Sagduyu, Yi Shi, Tugba Erpek
While there is a surge of interest to understand the security issues of machine learning, their implications have not been understood yet for wireless applications such as those in IoT systems that are susceptible to various attacks due the open and broadcast nature of wireless communications.
Spectrum Data Poisoning with Adversarial Deep Learning
no code implementations • 26 Jan 2019 • Yi Shi, Tugba Erpek, Yalin E. Sagduyu, Jason H. Li
We consider the case that a cognitive transmitter senses the spectrum and transmits on idle channels determined by a machine learning algorithm.
Deep Learning for Launching and Mitigating Wireless Jamming Attacks
no code implementations • 3 Jul 2018 • Tugba Erpek, Yalin E. Sagduyu, Yi Shi
An adversarial machine learning approach is introduced to launch jamming attacks on wireless communications and a defense strategy is presented.
Deep Learning Based MIMO Communications
no code implementations • 25 Jul 2017 • Timothy J. O'Shea, Tugba Erpek, T. Charles Clancy
We introduce a novel physical layer scheme for single user Multiple-Input Multiple-Output (MIMO) communications based on unsupervised deep learning using an autoencoder.
Information Theory Information Theory